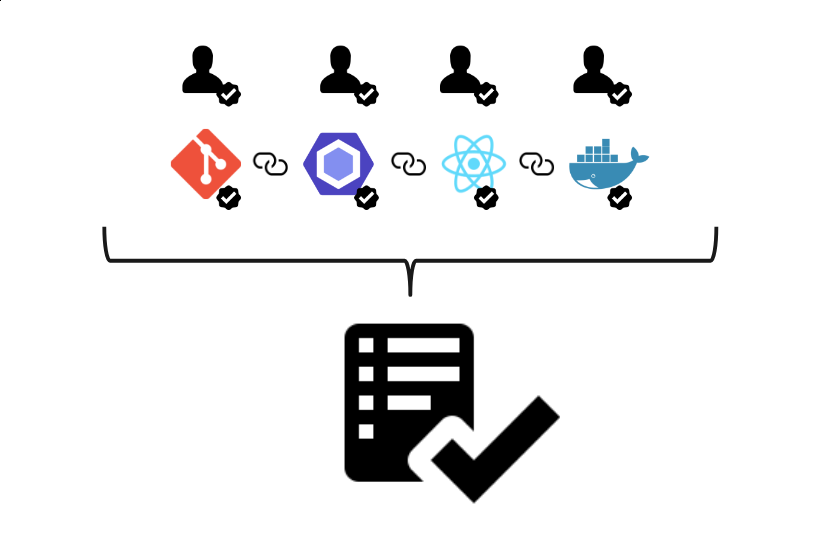
Software supply chain protection
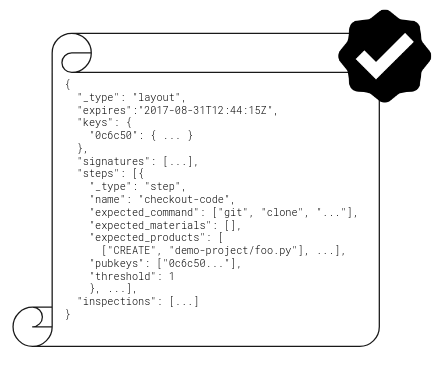
Supply chain compromises are becoming a frequent occurrence. In-toto can help you protect your software supply chain.
Read more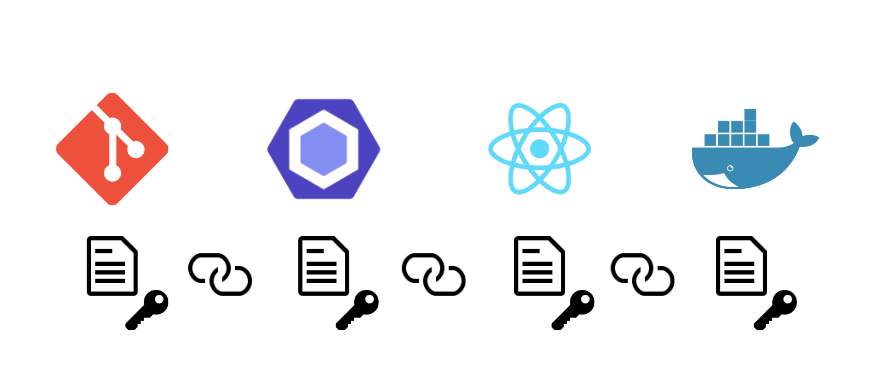
Open, Extensible Standard
in-toto is an open metadata standard that you can implement in your software's supply chain toolchain.